OFTP2 information
Logjam
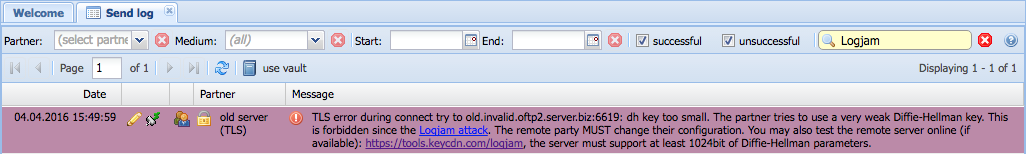
When communicating with an OFTP2 TLS server which is not offering a secure Diffie-Hellman key exchange, the following log message will be displayed if you are using a recent OS4X version:
Why does this happen after updating to a recent version of OS4X?
The situation has been rised since May 2015, when the Logjam attack became public. As a result, the minimum requirement for Diffie-Hellman keys in the TLS handshake has been rised to 768bits (valid until end-2015) up to 1024bits (since January 2016).
We are very keen about our objective to transmit files securely over the internet, and we cannot leave security behind just for cosmetic reasons. We live online security, so we want our customers to profit from a secure communication product.
In real-life situation, what is happening here?
If your system does not use a TLS cipher with
- Diffie-Hellman key exchange with a key size of at least 1024bits
- or -
- Elliptic curve Diffie–Hellman
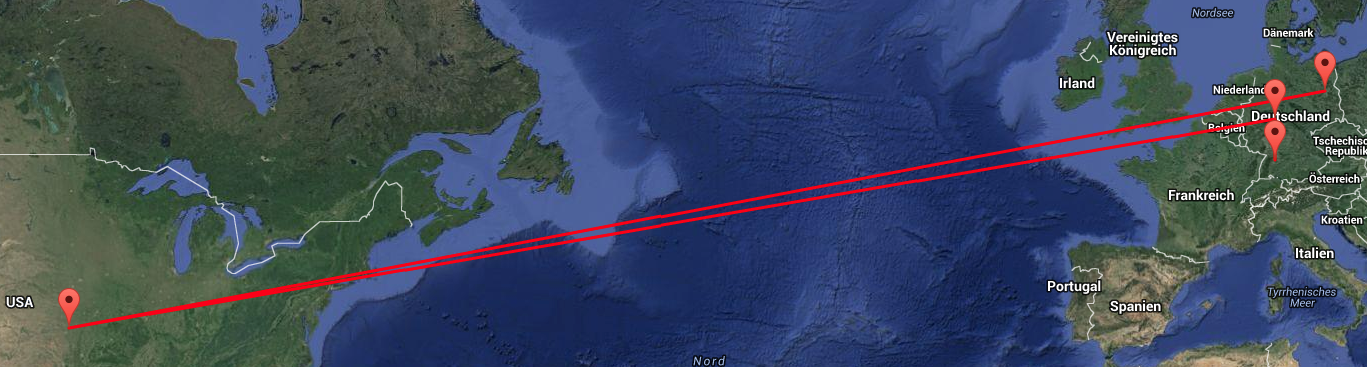
your communication can be hijacked and decrypted offline, so all your information and data is insecure. The following map shows the TCP/IP traffic from southern Germany to Berlin: it takes a route through the USA.
You may check your IP communication with traceroutes, resolve the hop IPs to geolocations and you'll get an impression about where your data packages are hijackable.
Solutions
There are several ways to overcome this situation:
Best solution: your communication partner offers a Diffie-Hellman key in the TLS handshake of appropriate size, currently more than 1024bits.
If the remote server uses a Diffie-Hellman key of at least 1024bits in size, you're actually safe and your communication cannot be decrypted as it is possible with a smaller key size. Perhaps the minimum value will rise in the future, so it's best to ask your partner for 1024bit and 2048bit DH keys.
Your communication partner offers a TLS cipher with Elliptic Curve Diffie-Hellman key exchange, which is not affected by this situation.
The rather new ECDHE ciphers used in TLS sessions are supported by OS4X, so you'll be able to use them with a higher priority if the remote party supports them.
On your own risk: you disable all ciphers using Diffie-Hellman key exchange.
Use this option by activating the configuration parameter "Configuration" -> "TLS" -> "Allow insecure downgrade of TLS cipher". You will be asked for the CVE number of the Logjam attack, so you need to learn about this situation in order to better decide if this solution is what you want. In this case, you disable all DH ciphers in the TLS handshake. A non-suppressible warning message will occur in every created session if a non-ECDHE cipher will be used in these TLS sessions.
Seeburger products
If your remote partner uses a Seeburger product (which is based on Java), he may disable all Diffie-Hellman ciphers by changing the following variable in his JRE security settings:
jdk.tls.disabledAlgorithms = DHE
External links
Our small explaining video is available at Youtube:
The full explanation about this situation is available here:
Additional information is available from these resources:
- openSSL's fast reaction on the Logjam attack
- openSSL's release notes starting with requirements of at least 1024bit DH keys
- Oracle's effort in requirements of at least 1024bit DH keys
Some external websites can be used to check if a weak DH key is in use with an OFTP2 server, if it's publically available over the internet, paste in the hostname like "my.oftp2-server.biz:6619":