PAM configuration for Windows Active Directory via SSSD
Declarations
In this documentation, several values will be used for hostnames, domain name, usernames and password. These are only examples and must be changed according to your environment.
AD server:
Hostname and aliases: 192.168.1.65
name alias: winad
local hostname seen from Windows side: dc.winad.c-works.net
Active directory domain name: winad.c-works.net
Kerberos realm: WINAD.C-WORKS.NET
(The kerberos realm is the domain name in upper case characters!)
User for connecting to domain (with administrative rights, but without permission to login interactively on AD server):
Username: pamauth Password: Test1234
User to be authentificated (as an example) and configured in OS4X:
Username: adUsername1 Password: OS4Xpwd
Username: os4x Password: Test1234
All commands on the Linux side are executed in the context of the user "root".
Installation
Install the necessary packages, for Debian and derivates the packages are sssd, adcli, realmd, oddjob, oddjob-mkhomedir and packagekit
apt install sssd adcli realmd oddjob oddjob-mkhomedir packagekit
Make sure DNS is pointing to your AD server(s) by checking /etc/resolv.conf and it having it contain an entry with an AD server IP, if it’s missing go ahead and add it, as the first entry.
systemd
If your network is managed by systemd, you cannot edit /etc/resolv.conf directly. Install resolvconf (if not already installed)
apt install resolvconf
Edit /etc/resolvconf/resolv.conf.d/head and add your AD: nameserver 192.168.1.65 and apply the change:
resolvconf --enable-updates resolvconf -u
Join AD
Now you can issue the realm join command with the domain name in order to join the domain.
realm join WINAD.C-WORKS.NET
It will default to use the Administrator user, add the -U flag to specify a different user account to join the domain.
realm join -U pamauth AD.EXAMPLE.COM
Now see if it works, and issue an id command.
id pamauth@WINAD.C-WORKS.NET
If you want to use short names, edit sssd.conf and set use_fully_qualified_names to false.
Advanced
sssd provides alternative directory servers modules, you can find detailed documentation in the official docs.
Configure PAM to use SSSD
Create or edit the file "/etc/pam.d/os4x" to contain the following line in order to allow OS4X PAM authentification to use SSSD (which now uses Active Directory):
auth required pam_sssd.so
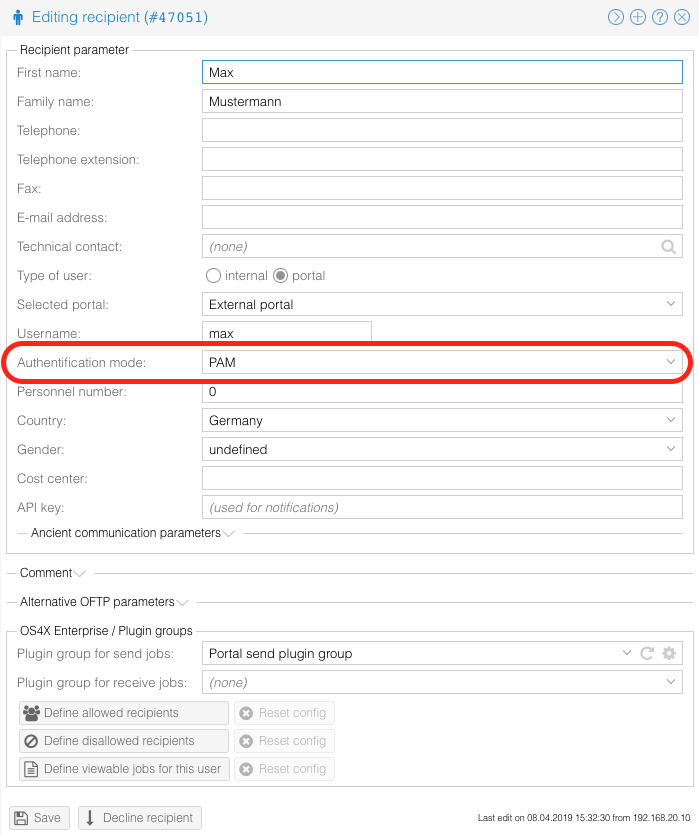
Configure user to authentificate via PAM
You can now configure your OS4X Webaccess users to use PAM as authentification method:
You can also use the username declaration including the domain name: